16 Aug Privileged Access Workstation (PAW) – Deep Dive and Practical Implementation
In our blog post from April 2021, we presented the basic principle of the Privileged Access Workstation (PAW) in detail. Now that we have had the opportunity to develop and implement PAW concepts for various other customers, we feel that the time has come to go into more detail about individual aspects and share our experiences with practical implementation.
Throwback
But first, a brief summary of the last blog: A PAW is used to separate the working environment for IT administrative activities from the classic “office” working environment for other activities. By defining the PAW as an independent system, it is possible to consistently implement this level of security required for IT administration. The encapsulation and hardening of the PAW results in robust protection against:
-
- Attacks from the Internet
- Attacks from your own network
- Manipulations in the supply chain
- Physical attacks
.
However, this hardening comes at the expense of usability and creates challenges in the daily use of PAW. That is why we want to devote more attention to these challenges in this issue.
Platform variants
Among the platform variants that are possible in principle, the following approach – separated into Tier0 and Tier1 – has proven successful in practice.
Tier0 PAW
As a rule, only a very small number of users (max. 10) are eligible to use Tier0 PAW. The particularly high level of protection requires a compromised implementation, which is why dedicated hardware is essential for these systems. The main argument here is the mandatory requirement to protect keystrokes from key logging (“clean keyboard policy”).
The PAW is often used exclusively as a client for remote access to a hardened Tier0 Terminal Server. Therefore, a standard-sized notebook is completely sufficient for the PAW. The terminal server (often also referred to as admin/jump server) is used for the actual administrative work and can only be accessed by the PAW of the same tier via the RDP protocol. Its consistent hardening and the higher costs associated with it are well invested. This is because the approach scales better with a changing number of users and improves protection against physical attacks.

Tier1 PAW
In many organizations, there is also a strict separation between Tier0 and Tier1 personnel. Therefore, the option of operating a virtual Tier1 PAW on a physical Tier0 PAW has little practical relevance.
The number of administrators and services as well as the share of administrative tasks in Tier1 is usually significantly higher than in Tier0. However, if the tiering model is applied consistently, a lower protection requirement may be assumed in Tier1, which in turn allows compromises in the implementation of the PAW.
Compromises are necessary primarily because many companies shy away from the high expense of deploying a large number of dedicated PAW systems. Also, the high proportion of administrative tasks in the course of a Tier1 admin’s day makes the permanent switch between PAW and office workstation an acceptance problem.
The Jump Server, which is proven in Tier0, is also not very practical due to the large number of Tier1 services and the different approaches to their administration, which also makes it a valuable target for attackers.
Therefore, we now recommend running the Tier1 PAW on dedicated hardware and the office workstation on the same, either:
-
-
- as a virtual machine (VM, see below) or
- as a virtual desktop (VDI) or on a terminal server (TS)
-
Hardening
The classic approach to hardening is to configure the GPO policies according to the specifications of an established vendor (e.g., Microsoft, CIS, or BSI). However, consistent enforcement of hardening with this approach can prove costly and unreliable if the OU or GPO structure is subject to frequent changes. We therefore continue to recommend the use of FBPro GmbH’s Enforce Suite for centrally controlled hardening of systems. This powerful tool has already been presented in detail in an earlier blog post. The included Enforce Administrator allows the selection and also the combination of hardening rules from different vendors and controls the application of hardening on the desired systems using PowerShell Desired-State-Configuration (DSC). This approach offers the following advantages:
-
-
- The curing can be rolled back at any time.
- Curing is applied cyclically (minimum: every 20 minutes) and thus remains permanently guaranteed.
- PowerShell DSC is built into Windows and requires no additional
-
.
If the focus is only on hardening the PAW configuration, Enforce TAP is used. As a partner of FBPro GmbH, we provide a PAW hardening set adapted to the respective customer situation as part of a project. However, hardening rules that are subject to frequent changes should then still be set via GPO.
More and more companies are obliged to comply with security requirements of the respective industry (e.g. ISO27001, TISAX etc.). These requirements always include the obligation to provide proof. The Enforce Administrator allows the hardening status of the managed systems to be checked at any time via dashboards and reports. In addition, the free AuditTAP has proven itself as a local solution for controlling and proving the hardening rules that have been set.
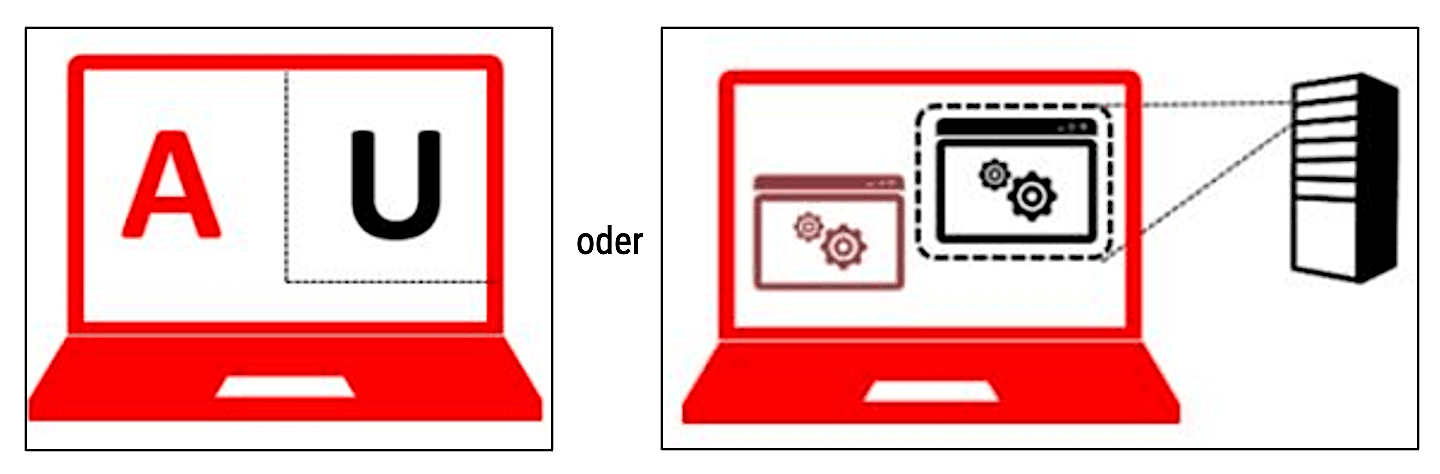
File Transfer
The solution for this task was already touched upon in the first blog on PAW. A hardened file server in the respective tier provides a file share that allows file transfer in only one direction at a time (from or to the respective tier), effectively a file in and a file out. The permissions of the respective user group must be limited to the necessary minimum. While one side may only place files on the share, the other side may only read and delete files on the same share. In addition, a scheduled task regularly clears up the objects whose wait time has been exceeded.
Remote Access
Internet access is taboo on the PAW. To ensure that remote access to the network is successful, an “always on” VPN is used. This ensures that all communication takes place via an encrypted tunnel and exclusively with the protected network. The decisive factor here is that authentication at the VPN gateway is possible via a computer certificate and thus the VPN tunnel is established immediately after the computer is started.
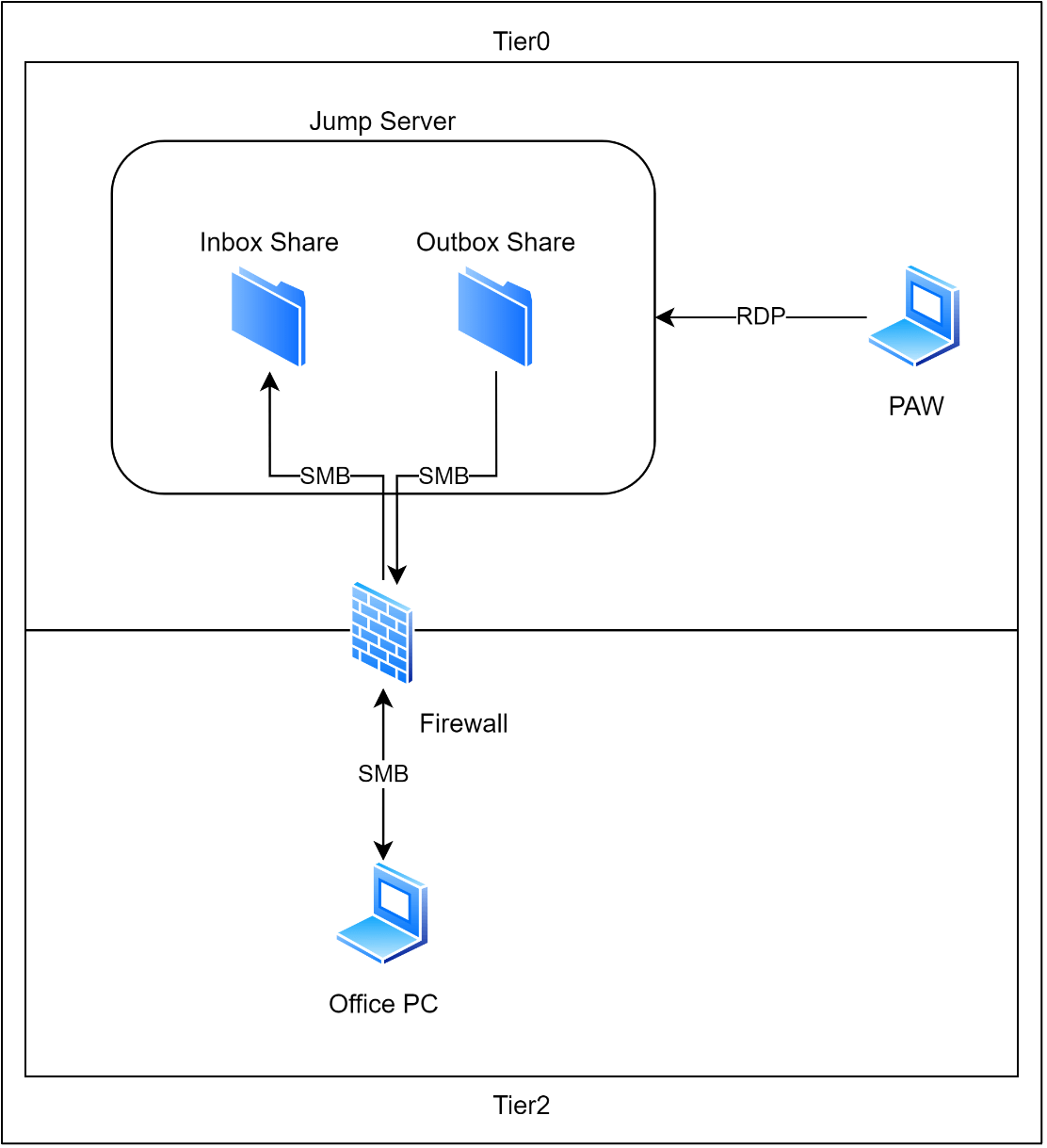
Screen Sharing
In order to show a third party (e.g. in case of support) the screen content of the PAW in a video conference, an HDMI capture device has proven to be a practical solution. The device is connected to the HDMI output of the PAW. It splits the incoming HDMI signal from the PAW to an HDMI and a USB output. The device is connected to the office workstation via this USB output, where it is recognized as a conventional webcam. In this way, the PAW’s screen output can be shared without delay in common video conferencing solutions, such as Microsoft Teams.
Suitable HDMI capture devices can be found under the search term “Game Capture Card” in established online retailers starting at about 40 euros.
Authentication via smartcard
In many cases, logging on to a Tier0 PAW is done with security-critical accounts, for example a domain admin account. The password can be read by observers, which is why additional security measures make sense at this level as well. Since fingerprint readers and cameras are not allowed to be used on a PAW, a smartcard solution – and specifically the YubiKey 5 NFC – has proven itself. The main advantages of this part are literally obvious:
-
- The device is small and robust and fits on any
- The certificates stored on the key are encrypted. If the key is lost, new certificates can be issued
- The installation and configuration of the key are possible with Windows on-board
- The key supports various protocols (PIV, FIDO2, OTP, OpenPGP, etc.) and offers storage capacity for multiple certificates. It can thus be used universally, e.g. for authentication at the VPN gateway, in a web application or as a second factor in Microsoft
- In addition to the certificate stored on the key, PIN entry and touch are used as further factors for secure
- In addition to the USB-A port for connection to the PAW, the Yubikey also has an NFC interface for authentication on mobile
- Removing the key from the device causes the system to be locked immediately or even the user to log off (GPO setting).
.
PAW Deployment
Since the number of systems and their complexity must remain manageable, especially in Tier0, the preparation and installation of PAW is usually done without the support of central management systems (such as Deployment Server, Endpoint Configuration Manager, etc. ). All the more reason to weigh the following points carefully:
Preparation of the installation routine
In addition to the usual tools for customizing a Windows image, a structured set of PowerShell scripts is used. These guarantee the necessary flexibility and limit the manual effort during the installation to the most necessary. Furthermore, they guarantee the consistent quality of the PAW configuration.
Every hour spent on preparing the PAW installation is therefore well invested, because it significantly reduces the effort (and possibly the hassle) during the subsequent installation and use. The initial effort for concept and piloting can quickly amount to 15-20 working days. The regular adaptation effort, however, is then less than 1 working day, including testing.
Teal has gained a lot of experience in this area over the years, which we are happy to put to the test in joint projects with you.
PAW (New) Installation
If the installation routine is well prepared, a PAW can be deployed within approx. 30-60 minutes. The provision of the PAW is fully automatic except for a few manual interventions. A new installation of the PAW is always necessary if the scope of functions or the configuration change significantly. This is the case, for example, when a new Windows feature pack is deployed or when the hardware model is changed.
In this respect, the reinstallation of a PAW every six months has become established.
PAW Updates
A WSUS in the corresponding tier is the first choice for the PAW update. The import of updates must be done daily for a PAW, but only the following update categories play a role:
-
- Critical updates
- Security updates
- Defender updates
.
Cloud PAW
As the importance of cloud services continues to grow, the topic of “cloud PAW” – the idea of running PAW in the cloud – remains a perennial issue. However, we have come to the conclusion that a PAW in the cloud violates the Clean Keyboard Policy as long as it is not controlled by a “classic” PAW in the same (or even higher) tier. In this exceptional case, however, the added value of a cloud system over the classical approach is lost.
If you have a viable approach to a PAW in the cloud, feel free to let us know 😊.
On the other hand, we can recommend a look at the following variant:
Single hardware PAW
As mentioned earlier, especially for Tier1 admins, running PAW on separate hardware can quickly become cumbersome and time-consuming. Frequent changes between systems and the need to work remotely can easily rob the approach of acceptance.
To address this, and yet not compromise the security of the PAW, running the office workstation in a VM on the PAW can be a viable option. Provided the hardware is sufficiently dimensioned and the office tasks do not become too resource-hungry, this approach can be the ideal solution.
Many use cases for the office workstation – such as participation in video conferences – require stable access to the hardware and connections of the underlying host. This requirement quickly separates the wheat from the chaff in the supposed multitude of virtualization solutions. We are not making a product recommendation at this point, but mention that in our experience the requirements can only be achieved with additional and commercial software.
All the functionalities and solutions described in the previous paragraphs are also possible with the single hardware PAW. File sharing is even much easier, because it is then done bi-directionally and directly between PAW and VM without increased risk.
Since the host’s hardware is shared with the VM, compromises are required in hardening (especially in disabling devices) as well as in handling network connections. Furthermore, a second network adapter is mandatory, which is then exclusively used by the VM. No WLAN connections are possible in the VM.
Compared to separate hardware, the additional costs for hardware and software with the single- hardware PAW remain manageable and are well invested. Because the result is satisfied admins who will quickly become friends with the approach 😊.
If we’ve piqued your interest and you’d like to get involved in a PAW project with Teal, we’d be happy to help.
Sieh dir diesen Beitrag auf Instagram an
Sieh dir diesen Beitrag auf Instagram an
LATEST POSTS
-
“Logging In Instead of Breaking In”: Why Your Identities Are the Biggest Security Risk
Attackers no longer “simply” break in, they LOG in. If you’re still relying on traditional defenses in 2026, we believe you’ve probably already lost the battle for your data....
01 April, 2026 -
Bye-bye, password frustration: Why TEAL is now going passwordless
As security consultants, we see every day that passwords are not only a security risk, but also slow you down massively in your everyday work. That's why we at TEAL have decided: ...
03 March, 2026 -
Look, a rainbow! – Why Google forces you to take action with NTLM
The alternative to NTLM* is called Kerberos and has been integrated into Active Directory since 2000. The most important difference to NTLM is the integration of a Key Distribution Center (KDC)...
02 February, 2026





























